Oops! Looks like you’ve taken a wrong turn.
No worries, though. While we couldn’t find that specific page, we’ve got plenty of electrifying content for you!
Check out our latest articles below. Dive in, click around, and enjoy the ride! 🚗⚡

Tesla Wall Charger Troubleshooting: Reset To Start Tesla Charging
Erwin MeyerAre you tired of your Tesla Wall Charger not working properly? Do you find yourself constantly resetting it or struggling to connect your vehicle to it? You’re not alone. The Tesla Wall Charger is a crucial component for charging your electric vehicle, and when it’s not functioning correctly, it can…

Tesla Glass Roof: Options Available on Teslas
Erwin MeyerTeslas are the most technically advanced cars in the world. Everything down to the glass roof was thoroughly developed, tested, and then upgraded. All current Tesla models come standard equipped with glass roofs. Tesla offered a panoramic sunroof and a solid roof as options for the Model S in the…
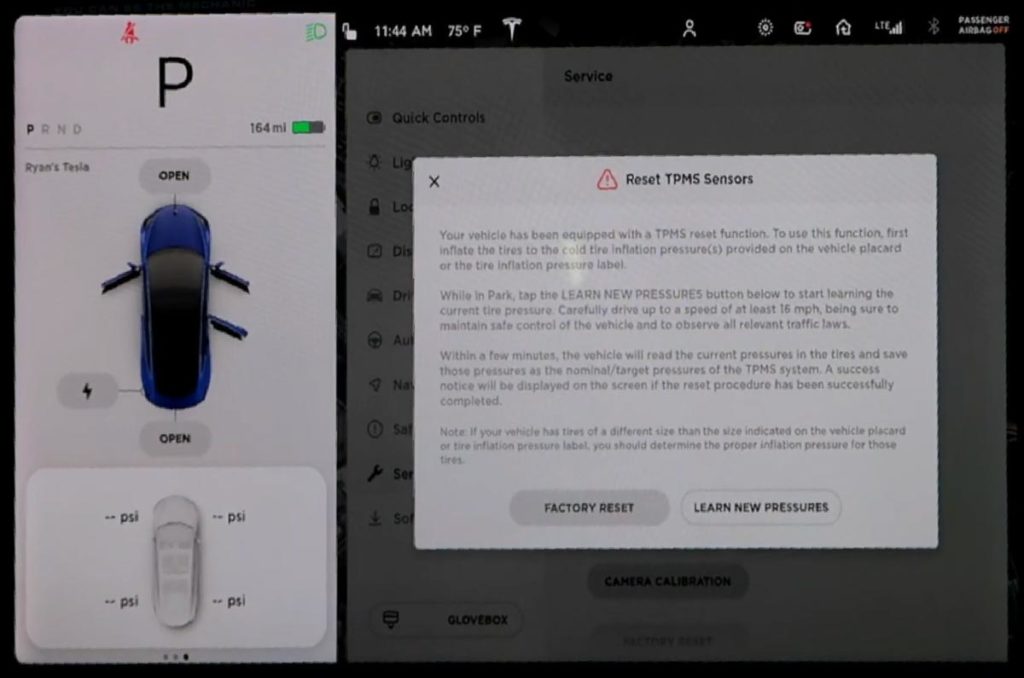
How To Reset Tesla Tire Pressure: All Questions Resolved
Erwin MeyerThe Tire Pressure Monitoring System on Teslas consists of pressure sensors inside the tires that relay information to your touchscreen. The system alerts you when the pressure in the wheel gets too high or too low. Here’s how to reset Tesla tire pressure sensors in two ways: Use the touchscreen…

Tesla Roadside Assistance vs AAA Compared 2023
Erwin MeyerTesla Roadside Assistance and AAA are two of the most popular roadside assistance programs that offer services to drivers with car trouble. However, first-time Tesla customers often find it difficult to choose between the two. This article will compare Tesla Roadside Assistance and AAA to help you decide which is…

What’s the Ideal Tesla Battery Temperature Range? Temperatures And Effects
Erwin MeyerTesla’s introduction of electric vehicles has created a frenzy globally. With the exacerbation of climate change and its effects, most people prefer electric-powered cars to conventional cars. However, Tesla’s susceptibility to temperature changes remains its Achilles heel. So, what exactly is the ideal Tesla battery temperature range? The ideal Tesla…

How To Upgrade Tesla Model 3 Audio: Should You Upgrade Your Sound?
Erwin MeyerDid you know that upgrading the audio system in your Tesla Model 3 can take your listening experience to the next level? The factory sound system is decent, but for true music enthusiasts, it may not be enough. If you’re considering upgrading your audio system, it’s important to understand your…




